
Securing the Future,
Together.
We are dedicated to building a safer digital world through education, innovation, and unwavering integrity.
We Are CYBERLIT.
Cyber security is not a one‑time activity. Threats evolve constantly, and organisations must adapt just as quickly.
CyberLit’s security specialists perform a comprehensive review of your IT ecosystem. Following the assessment, we deliver a practical roadmap tailored to your business, outlining prioritised actions to uplift your cyber security maturity using the NIST framework — scalable for organisations of all sizes.
Our Mission


To empower organizations with the knowledge and tools to defend against evolving cyber threats.




Our Vision
A world where digital safety is a fundamental standard, not a luxury.
Integrity, Innovation, Excellence, and Collaborative Growth.
Core Values
Why a Cyber Security Risk Assessment Matters?
A structured cyber security assessment enables you to understand where your business is exposed and how to address those risks effectively.
Key benefits include:
Identifying vulnerabilities before attackers exploit them
Strengthening existing security controls and processes
Improving governance, resilience, and cyber maturity
Supporting compliance with data protection and security standards






Essential Eight Compliance Assessment
The Essential Eight are a set of cybersecurity strategies developed by the Australian Government to help organisations improve their cybersecurity posture.
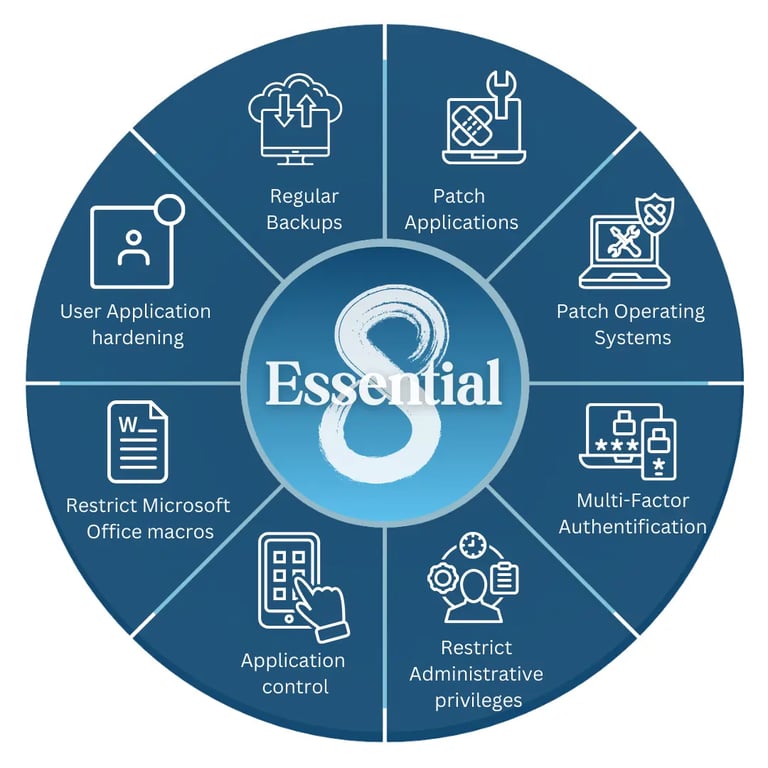

Patch Applications: Keep your software up-to-date to block known weaknesses hackers use.
Patch Operating Systems: Regularly update your operating system (e.g., Windows, macOS) for maximum protection.
Configure Microsoft Office Macro Settings: Configure Microsoft Office to block harmful programs hidden in documents.
User Application Hardening: Limit unnecessary features in commonly used programs, reducing potential risks.
Restrict Administrative Privileges: Restrict who has full control over your systems, minimising damage from compromised accounts.
Multi-Factor Authentication: Use multi-factor authentication (MFA) to require more than just a password to log in.
Application Control: Only allow approved programs to run, preventing unauthorized software from causing harm.
Regular Backups: Regularly back up your data so you can recover it quickly in case of an attack
CyberLit assesses your current maturity level against these controls and provides clear recommendations to improve compliance
These eight strategies focus on key areas to mitigate risks from cyberattacks.
What CyberLit Offers ?
Simulated Attacks
Realistic phishing & social engineering tests to evaluate staff readiness.
Interactive Training
Bite-sized, scenario-based lessons that stick.
Risk Scoring
Identify your most vulnerable departments or individuals.
Progress Tracking
See awareness improve over time, backed by real data.
Bridging Cybersecurity Gaps
Security-First Mindset
We practice what we preach. Security isn't just a product; it's ingrained in our DNA and every operation.
Continuous Development
In a rapidly changing industry, we prioritize constant learning and upskilling for our entire team.


A Culture of Excellence
Our Methodology
Precision in Training & Assessment
Evidence-Based Curriculum
Our training materials are continuously updated based on real-time threat intelligence and actual breach data.
Rigorous Assessment Standards
We utilize industry-standard frameworks (NIST, ISO 27001, Essential 8) to provide objective, actionable assessments.
Measurable Outcomes
We focus on quantifiable improvements in security posture, moving beyond compliance boxes to actual risk reduction.


FAQs
What do you do?
We identify weak spots and offer practical cybersecurity recommendations.
Who benefits most?
Organizations wanting to build a strong security culture from the ground up.
How do you simplify cybersecurity?
By bridging complex standards with real-world application, making security practical.
What’s your mission?
To cut through noise and reduce human-related cyber risk effectively.
How do you help users?
We focus on the keyboard—where most cyber risks actually happen.
Can you tailor recommendations?
Yes, all advice is practical and customized to fit your specific business needs.

Contact Us
Reach out for cybersecurity training and awareness.
Cyberlit
Empowering organizations with industry-leading cybersecurity training and assessment solutions.
Contact
Email - info@cyberlit.com.au
Phone - 08 6248 8275
